Patch Management
Stay ahead of vulnerabilities with ITarian’s automated Patch Management solution—your first line of defense against cyber threats. Detect, assess, and deploy patches seamlessly across all endpoints, ensuring your IT infrastructure remains secure, compliant, and up to date. Minimize downtime, eliminate security gaps, and take control of software updates with real-time insights and centralized management. Protect your business with efficient, automated patching—so you can focus on what matters most.
Comprehensive Patch Management System for Any IT Environment
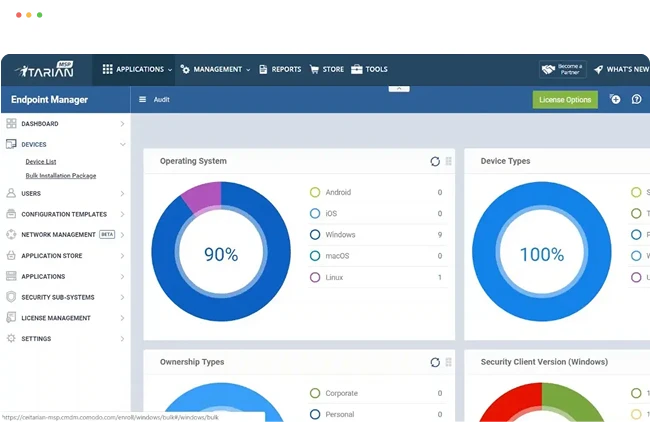
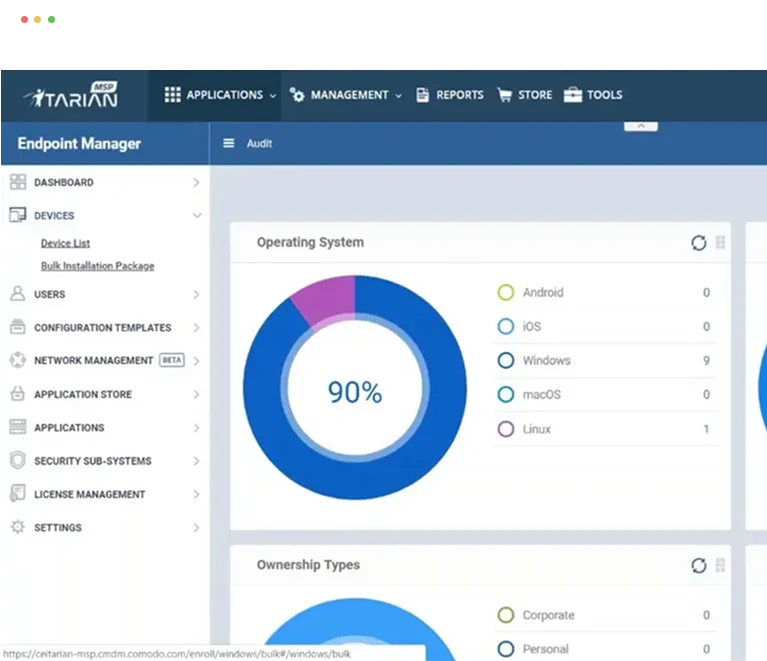
No matter your IT setup, ITarian’s versatile Patch Management solution ensures every device stays updated and secure. From Windows, macOS, and Linux to third-party applications, our automated system detects vulnerabilities, prioritizes critical updates, and deploys patches seamlessly. Whether managing a small business network or a large enterprise infrastructure, our centralized platform gives you full control, real-time reporting, and compliance assurance—all with minimal disruption to your operations.
- Real-time monitoring of endpoints, servers, and networks
- Automated alerts for hardware, software, and security issues
- Centralized dashboard for complete IT visibility
- Secure, on-demand remote access to endpoints, servers, and IT systems
- Granular permissions and session logging for compliance and security
- Seamless file transfer and remote troubleshooting for efficient IT support
- Automated deployment of OS and third-party software patches
- Real-time vulnerability detection and compliance reporting
- Centralized control to schedule and enforce updates across all devices
- Automate routine IT tasks to improve efficiency and reduce manual workload
- Deploy custom scripts for troubleshooting, maintenance, and configuration
- Schedule and execute automated workflows across multiple endpoints
- Real-time tracking of hardware, software, and network assets
- Automated inventory updates for complete IT asset visibility
- Detailed reporting for compliance, lifecycle management, and cost optimization
- Generate real-time reports on system health, security, and performance
- Customizable dashboards for data-driven IT decision-making
- Automated alerts and trend analysis for proactive issue resolution
Patch Management Benefits to Your BusinessITarian’s Patch Management solution helps businesses stay secure, compliant, and efficient by automating the detection and deployment of critical updates. By proactively patching vulnerabilities, you can reduce security risks, prevent cyber threats, and minimize downtime caused by outdated software. With centralized control, real-time monitoring, and seamless integration with IT management tools, you gain enhanced operational efficiency while ensuring compliance with industry regulations. Keep your IT infrastructure resilient, protect sensitive data, and free up IT resources to focus on strategic business initiatives—all with a smart, automated patching solution.
Get Started for Free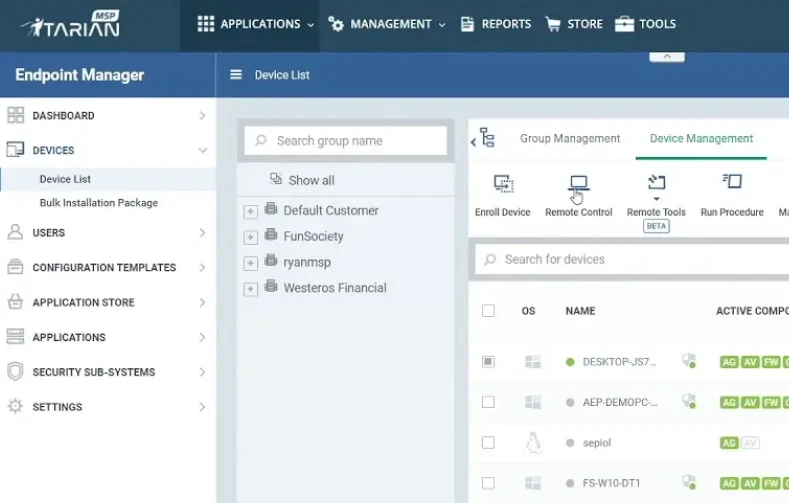
Testimonials
"We are a small managed service provider in the U.K. that focuses on serving our customers with the very best IT experience possible - be that computer repairs, maintenance or security. We are currently taking full advantage of the remote management and monitoring module of ITarian, which enables us to monitor our customers and service them faster. By having access to a proven,service management tool like ITarian, we can grow our business by automating tasks without sacrificing service or performance."
"The business around Aquaflam is built in part around our ability to service our customers remotely and ensure there is never any down time with our service calls, our maintenance, or our upgrades to customers. The ITarian platform is a great opportunity for us as a small business to take full advantage of a free, proven, secure RMM technology that we think will help us to monitor and service our customers better."
“ITarian is giving us better utilization of our internal resources, freeing up time to focus on additional customer challenges and solve them quickly –and, we’re saving money because it is all free. We can now move our break fix customers to a managed services model that will generate new revenue streams for us. We look forward to a very long relationship with ITarian and helping them to continue to make ITarian a success for all."
"Évolur is an early adopter of the ITarian platform. We are very pleased with the flexibility and options that platform gives us, to help service our customers better. We are already starting to leverage the remote monitoring and management capabilities within ITarian MSP, which has been very intuitive and easy to use. We look forward to leveraging more of the platform in the months to come."
Many customers of Marly Computers vof are small to medium sized businesses, who truly appreciate our hands-on and dedicated approach we take to solve their IT challenges. Our technical team is always on the road helping our clients, and the lack of a remote management and monitoring system in place always created a challenge for us. Since taking advantage of ITarian's remote management features and offerings, we started seeing faster response times, quicker remediation and improved management of our customers. We are very happy to be an early adopter of the ITarian managed services platform and look forward to exploring more of its offerings in the months to come."
“The money we are saving on licensing fees and other service costs through the ITarian MSP allows us to hire more people and better compete for business. ITarian MSP is an excellent solution that meets our RMM needs. The fact that there are additional features being added to the platform in the months to come allows us to focus on continued growth while also solidifying the customer relationships we have worked so hard to build."
Why Choose ITarian?
ITarian’s Patch Management ensures your systems stay secure, up to date, and compliant with minimal effort. With automated deployment, real-time monitoring, and seamless rollback options, you gain full control over your patching process.
