Secure Ways to Access Another Computer Using Remote Desktop
Updated on November 27, 2025, by ITarian
In today’s hybrid and remote work environments, knowing how to remote desktop to another computer has become an essential skill for IT teams, cybersecurity professionals, system administrators, and business leaders who need secure access to critical systems. Whether you’re supporting employees, managing servers, resolving technical issues, or accessing your own workstation from a different location, remote desktop access enables seamless connectivity from virtually anywhere. But these connections must be secure, efficient, and compliant with modern cybersecurity standards to protect sensitive data and ensure uninterrupted workflows.
Understanding how to set up, configure, and secure remote desktop access is now crucial for organizations of all sizes. Remote access offers convenience, but it also introduces risks if not managed properly—including unauthorized entry, brute-force attacks, and RDP vulnerabilities. In this comprehensive article, we’ll cover everything you need to know about safely connecting to another computer using Remote Desktop, from setup fundamentals and network configurations to security best practices and troubleshooting. By the end, you’ll have a complete understanding of both the technical and security aspects to make remote access a dependable part of your IT strategy.
What Remote Desktop Access Actually Is
Remote desktop access allows a user to connect to a computer over a network as if they were sitting in front of it physically. Windows Remote Desktop Protocol (RDP), remote desktop apps, VPN tools, and third-party platforms make this possible.
With remote desktop access, users can:
-
Control applications and files
-
Run administrative tasks
-
Access servers and internal systems
-
Support users remotely
-
Monitor system performance
-
Execute troubleshooting operations
This functionality makes remote troubleshooting, remote work, and enterprise IT management significantly more efficient.
Why Remote Desktop Access Is Essential for Modern IT Operations
Remote desktop technology isn’t just a convenience—it’s a necessity. As companies move toward distributed teams, cloud adoption, and device-agnostic workflows, remote access supports:
Critical business use cases:
-
Remote IT support for employees
-
Access to internal systems securely
-
Server maintenance without physical presence
-
Virtualized work environments
-
Rapid response during technical incidents
-
Support for multi-location operations
Without secure remote desktop capabilities, organizations face inefficiencies, delays, and increased operational risk.
Key Methods for Remote Desktop Access
There are several ways to remote desktop to another computer, each offering different levels of security, ease of use, and administrative control.
Using Windows Remote Desktop Protocol (RDP)
RDP is the most common and built-in method used across Windows devices.
Benefits:
-
Installed by default on Windows
-
Supports encrypted connections
-
Offers remote control over the entire desktop
-
Integrates with Active Directory
However, RDP must be configured carefully due to its common exploitation by cybercriminals.
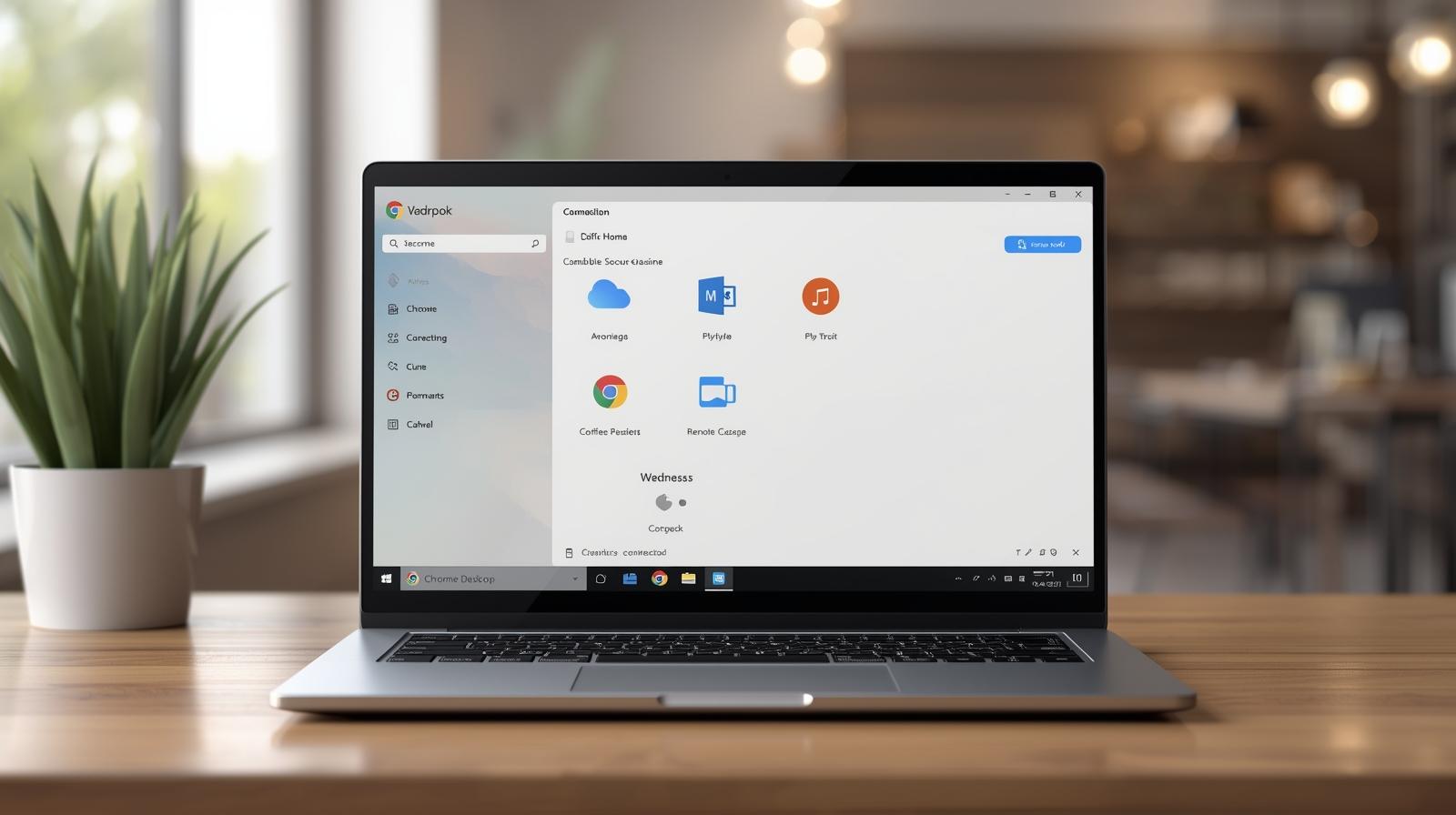
Using Third-Party Remote Access Tools
Many organizations rely on alternative tools for additional features or easier setup.
Popular remote access tools include:
-
AnyDesk
-
TeamViewer
-
Chrome Remote Desktop
-
Splashtop
-
VNC platforms
These are helpful when cross-platform access or cloud-based connectivity is needed.
Using VPNs for Secure Remote Connection
A VPN allows secure access to internal networks, providing an additional layer of protection before connecting via RDP.
Benefits of VPN-based remote access:
-
Strong encryption
-
Restricted access to internal resources
-
Reduced exposure to open internet threats
-
Better compliance posture
VPN + RDP is one of the safest combinations for enterprise use.
Cloud-Based Remote Work Platforms
Solutions like Microsoft Azure Virtual Desktop or Windows 365 Cloud PC provide remote access via cloud-hosted environments.
Advantages include:
-
Simplified management
-
High security
-
Scalable virtual desktops
-
Centralized software control
These platforms are ideal for large enterprises or high-security environments.
Preparing a Computer for Remote Desktop Access
Before you can remote desktop to another computer, several steps must be taken to ensure it is accessible, secure, and properly configured.
Enabling Remote Desktop on Windows
You must enable remote access settings on the target machine.
Steps typically include:
-
Opening System Settings
-
Allowing Remote Desktop connections
-
Enabling Network Level Authentication
-
Adding permitted users
This ensures only authorized individuals can connect.
Setting Up Firewall Permissions
Windows Firewall must be configured to allow RDP traffic.
This includes:
-
Allowing inbound RDP connections
-
Limiting access to approved IP addresses
-
Setting port forwarding rules for external connections
Firewall configurations are essential for security.
Configuring Router Port Forwarding (For Home or Small Office Networks)
If connecting from outside a private network, RDP ports may need to be forwarded.
Key considerations:
-
Forwarding port 3389
-
Mapping external ports to internal devices
-
Avoiding unnecessary exposure to the internet
Port forwarding should always be paired with VPN access where possible.
Using Strong Authentication and Secure Passwords
RDP is frequently attacked through brute-force methods, so authentication must be strong.
Best practices include:
-
Using long, complex passwords
-
Enabling Multi-Factor Authentication (MFA)
-
Avoiding shared accounts
-
Disabling unused local accounts
Stronger authentication dramatically reduces risk.
IP Restrictions and Network Layer Controls
Restricting remote desktop access to specific IP addresses prevents unauthorized attempts.
Ways to restrict access:
-
Firewall allow-lists
-
VPN-only access
-
Network segmentation
-
Zero Trust access controls
IP filtering is one of the most effective security measures for remote access.
Using Remote Desktop to Access Another Computer
Once the configuration is complete, you can connect from another device.
Typical steps include:
-
Opening the Remote Desktop Connection app
-
Entering the target computer’s IP address
-
Providing credentials
-
Accepting the security prompt
-
Controlling the remote machine
Organizations may automate or streamline these processes using device management tools.
Security Risks Associated With Remote Desktop Access
While remote desktop technology is powerful, it must be handled carefully to prevent security vulnerabilities.
Common risks:
-
Brute-force login attempts
-
Exposed RDP ports
-
Outdated authentication
-
Unpatched systems
-
Weak or reused passwords
-
Stolen credentials
-
Man-in-the-middle attacks
Cybercriminals frequently target RDP because it gives direct access to systems.
Best Practices for Securing Remote Desktop Access
To protect devices and networks, IT teams must implement multiple layers of defense.
Require Multi-Factor Authentication
MFA stops attackers even if passwords are compromised.
Restrict Access Using VPNs
VPNs limit exposure and ensure only trusted users can attempt remote access.
Use Network Level Authentication (NLA)
NLA prevents full RDP sessions until the remote user is authenticated.
Change the Default RDP Port
Although not a primary security measure, changing the port reduces automated scanning.
Apply Regular Updates and Patches
Updates protect against:
-
RDP vulnerabilities
-
Privilege escalation exploits
-
Zero-day attacks
Patch management is non-negotiable.
Disable Remote Access When Not Needed
Attack surfaces should remain as small as possible.
Limit Administrative Privileges
Admin abuse is one of the leading causes of major breaches.
Monitor Logs and Access Attempts
Threat detection relies on:
-
Reviewing login attempts
-
Identifying repeated failures
-
Spotting unusual geographic access patterns
Monitoring helps detect suspicious behavior early.
Remote Desktop Access for Enterprise IT Teams
Large organizations use remote desktop capabilities to support distributed environments.
Enterprise benefits:
-
Scalability
-
Centralized security
-
Role-based access
-
Granular control
-
Automation for remote tasks
Enterprise RDP access must comply with industry regulations and internal governance.
Remote Desktop Access for MSPs and IT Service Providers
Managed Service Providers rely heavily on remote desktop tools.
MSP benefits include:
-
Quick troubleshooting
-
Reduced on-site visits
-
Centralized device management
-
Automated monitoring
-
Remote software updates
RDP simplifies client support operations when combined with strong security.
Troubleshooting Common Remote Desktop Issues
Even with proper setup, remote desktop connections may fail. Common issues include:
Incorrect IP or Hostname
Verify the address and remote settings.
Firewall Blocking
Ports may not be configured correctly.
Network Issues
Weak or unstable connectivity blocks remote access.
Disabled Services
RDP or necessary protocols may be turned off.
Expired Credentials
Passwords or accounts may need updating.
Unsupported Versions
Old Windows versions may require compatibility adjustments.
Troubleshooting ensures a reliable remote access experience.
Frequently Asked Questions
1. Is remote desktop access secure?
Yes, when combined with VPN, MFA, and strict authentication controls.
2. Do I need to open port 3389 for RDP?
Only if accessing externally—but VPN-based access is recommended instead.
3. Can I remote desktop to a computer from a different network?
Yes, using VPN, cloud platforms, or properly configured port forwarding.
4. Do macOS and Linux support remote desktop?
Yes—through dedicated RDP clients and third-party tools.
5. What’s the safest way to use remote desktop?
With VPN, MFA, encryption, device compliance, and proper firewall rules.
Final Thoughts
Remote desktop access has become an essential tool for IT teams, remote employees, and organizations that require fast, efficient, and secure access to systems from anywhere. Knowing how to remote desktop to another computer is only the beginning—true security comes from implementing strong authentication, VPN restrictions, encryption, and ongoing monitoring. With a combination of best practices and modern automation, remote access can remain both powerful and safe for business environments of any size.
If you’re ready to elevate remote access security, streamline system management, and improve IT control, you can Start your free trial with ITarian and explore advanced tools designed to simplify secure remote device management.