Strengthening IT Security with Cybersecurity Tool Integrations
Updated on April 17, 2026, by ITarian
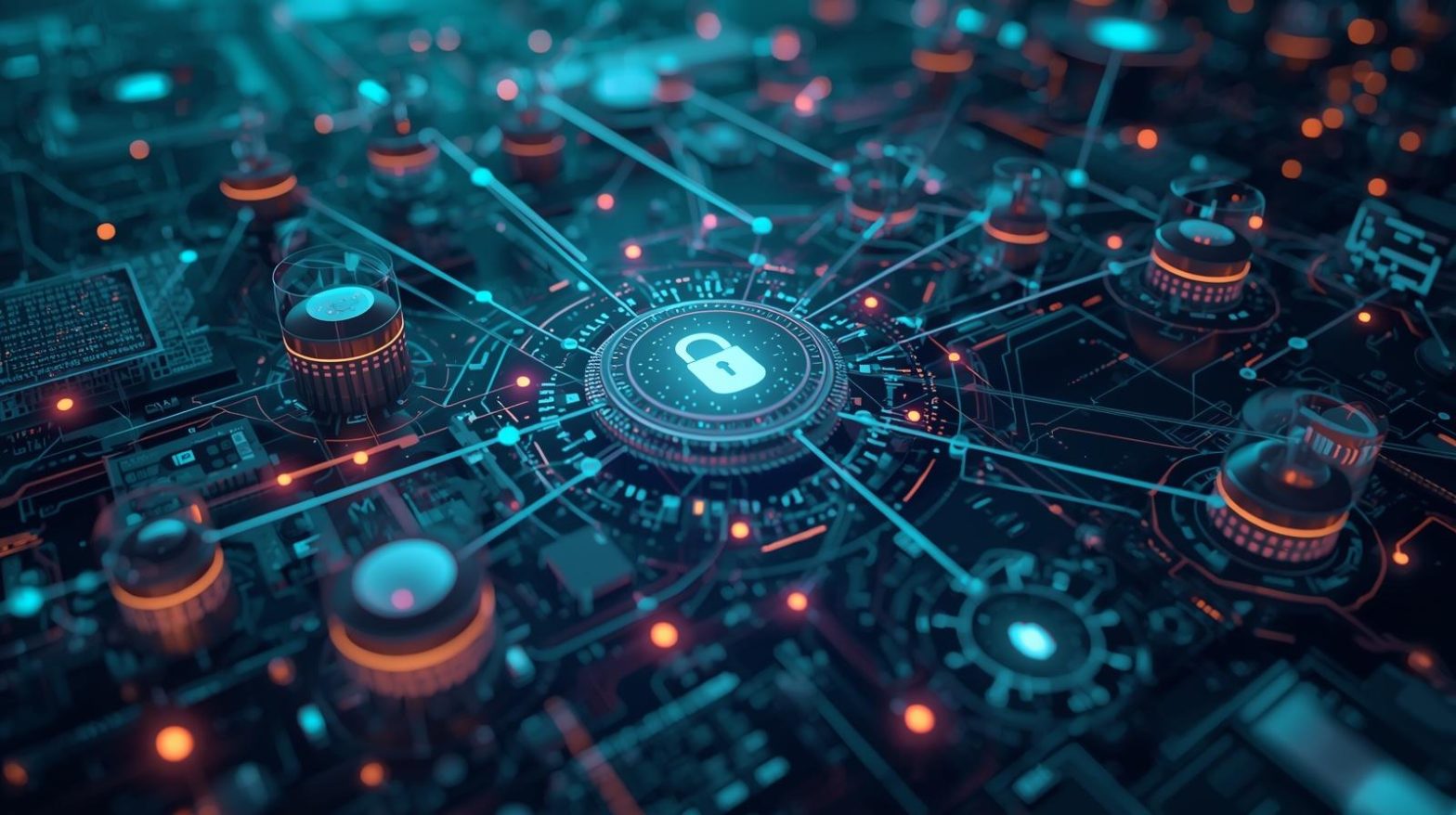
Are your security tools working together—or operating in silos? Many organizations invest heavily in cybersecurity solutions, yet still struggle with gaps in visibility and slow response times. This is where cybersecurity tool integrations become critical. By connecting multiple security systems into a unified ecosystem, organizations can improve efficiency, enhance threat detection, and reduce response times. For IT managers, cybersecurity professionals, and business leaders, cybersecurity tool integrations are no longer optional—they are essential for building a resilient and scalable security strategy in today’s complex threat landscape.
What are Cybersecurity Tool Integrations
Cybersecurity tool integrations refer to the process of connecting different security tools and platforms so they can share data, automate workflows, and work together seamlessly. Instead of operating independently, integrated systems provide a centralized and coordinated approach to security.
For example, integrating endpoint security with SIEM tools allows faster threat detection and response. Similarly, combining firewalls, identity management systems, and monitoring tools improves overall visibility.
Key functions of cybersecurity tool integrations include:
- Data sharing between tools
- Centralized monitoring and control
- Automated incident response
- Improved threat intelligence correlation
- Streamlined workflows
With cybersecurity tool integrations, organizations can move from reactive to proactive security operations.
Why Cybersecurity Tool Integrations Matter Today
Modern IT environments rely on multiple security solutions, each addressing specific threats. However, without integration, these tools may create gaps instead of closing them.
Eliminating Security Silos
Disconnected tools limit visibility and slow down response times.
Faster Threat Detection
Integrated systems can correlate data and identify threats more quickly.
Improved Incident Response
Automation enables immediate action when threats are detected.
Enhanced Visibility
Centralized dashboards provide a comprehensive view of security posture.
Better Resource Utilization
IT teams can manage security more efficiently without duplication of effort.
For CEOs and founders, cybersecurity tool integrations ensure stronger protection while optimizing operational costs.
Core Components of Cybersecurity Tool Integrations
To implement effective integrations, organizations must focus on several key components.
API Connectivity
Application Programming Interfaces (APIs) enable tools to communicate and share data.
Data Normalization
Standardizing data formats ensures compatibility between systems.
Centralized Dashboards
Unified dashboards provide a single view of all security activities.
Automation Workflows
Automated processes enable faster response to security events.
Threat Intelligence Sharing
Integration allows real-time sharing of threat intelligence across platforms.
These components create a cohesive and efficient security ecosystem.
Common Use Cases of Cybersecurity Tool Integrations
Cybersecurity tool integrations can be applied across various security operations.
SIEM and Endpoint Integration
Combining SIEM integration solutions with endpoint tools enhances threat detection.
Identity and Access Management Integration
Ensures secure access control across systems.
Vulnerability Management Integration
Integrates scanning tools with patch management systems.
Incident Response Automation
Triggers automated actions when threats are detected.
Cloud Security Integration
Monitors and secures cloud-based environments.
These use cases demonstrate how integration improves overall security effectiveness.
Benefits of Cybersecurity Tool Integrations Across Industries
Cybersecurity tool integrations deliver value across multiple sectors.
Healthcare
- Protects sensitive patient data
- Enhances compliance with regulations
- Improves threat detection
Finance
- Secures financial transactions
- Prevents fraud
- Supports regulatory compliance
Retail
- Protects customer data
- Ensures secure payment systems
- Reduces downtime
Manufacturing
- Secures operational technology
- Prevents disruptions
- Enhances efficiency
Education
- Protects student data
- Supports secure digital learning
- Improves network visibility
For IT leaders, cybersecurity tool integrations ensure consistent and scalable protection.
Challenges in Implementing Cybersecurity Tool Integrations
While integrations offer significant benefits, organizations may face challenges.
Compatibility Issues
Different tools may not integrate بسهولة due to varying standards.
Data Overload
Large volumes of data can overwhelm systems and teams.
Security Risks
Improper integration can introduce vulnerabilities.
Resource Constraints
Integration requires time, expertise, and investment.
Maintenance Complexity
Integrated systems require ongoing management and updates.
Addressing these challenges requires careful planning and the right tools.
Best Practices for Effective Cybersecurity Tool Integrations
To maximize the value of cybersecurity tool integrations, organizations should follow best practices.
Choose Compatible Tools
Select solutions that support integration and open APIs.
Prioritize Critical Integrations
Focus on high-impact areas such as threat detection and response.
Use Automation
Leverage cybersecurity automation tools to streamline workflows.
Monitor Integration Performance
Continuously evaluate integration effectiveness.
Maintain Security Standards
Ensure integrations do not compromise security.
Train IT Teams
Equip staff with the skills needed to manage integrated systems.
These practices help create a reliable and efficient integration strategy.
Role of Automation in Cybersecurity Tool Integrations
Automation is a key driver of successful integrations. It improves efficiency and reduces manual effort.
Key benefits include:
- Real-time threat detection and response
- Automated data correlation
- Faster incident resolution
- Reduced human error
- Improved scalability
Automation enables organizations to manage complex security environments effectively.
How to Implement Cybersecurity Tool Integrations Successfully
A structured approach ensures effective implementation.
Step 1: Assess Current Security Tools
Identify existing tools and integration capabilities.
Step 2: Define Objectives
Set clear goals for integration, such as improving visibility or response time.
Step 3: Select Integration Platforms
Choose platforms that support seamless connectivity.
Step 4: Develop Integration Workflows
Design workflows for data sharing and automation.
Step 5: Test Integrations
Validate functionality in a controlled environment.
Step 6: Monitor and Optimize
Continuously refine integrations based on performance.
Following these steps helps organizations build a strong integration framework.
Future Trends in Cybersecurity Tool Integrations
The future of cybersecurity is increasingly integrated and automated.
AI-Driven Security Integration
Artificial intelligence enhances threat detection and decision-making.
Unified Security Platforms
Organizations are adopting unified security management systems.
Cloud-Based Integration
Cloud platforms offer scalability and flexibility.
Real-Time Threat Intelligence
Advanced tools provide instant insights into threats.
Zero Trust Integration
Integration supports zero trust security models.
Staying ahead of these trends helps organizations remain competitive.
Actionable Tips to Improve Cybersecurity Tool Integrations
If you want to enhance your integration strategy, consider these practical tips:
- Identify gaps in your current security ecosystem
- Use centralized platforms for integration
- Automate repetitive security tasks
- Monitor integration performance regularly
- Train IT staff on integration tools
- Continuously update and optimize workflows
These steps help ensure effective and efficient security integration.
Frequently Asked Questions
Q1: What are cybersecurity tool integrations?
Cybersecurity tool integrations connect multiple security tools to improve visibility and efficiency.
Q2: Why are integrations important in cybersecurity?
They enhance threat detection, improve response times, and reduce security gaps.
Q3: What tools can be integrated?
Tools such as SIEM, endpoint security, IAM, and vulnerability management systems can be integrated.
Q4: Can small businesses benefit from integrations?
Yes, integrations help organizations of all sizes improve security and efficiency.
Q5: How does automation improve integrations?
Automation enables faster data processing, threat detection, and incident response.
Final Thoughts
Cybersecurity tool integrations are transforming how organizations approach security. By connecting tools, automating workflows, and improving visibility, businesses can build stronger and more resilient defenses. For IT managers, cybersecurity professionals, and business leaders, adopting an integrated approach is essential for staying ahead of evolving threats. As technology continues to advance, organizations that prioritize cybersecurity tool integrations will be better equipped to protect their systems and data.