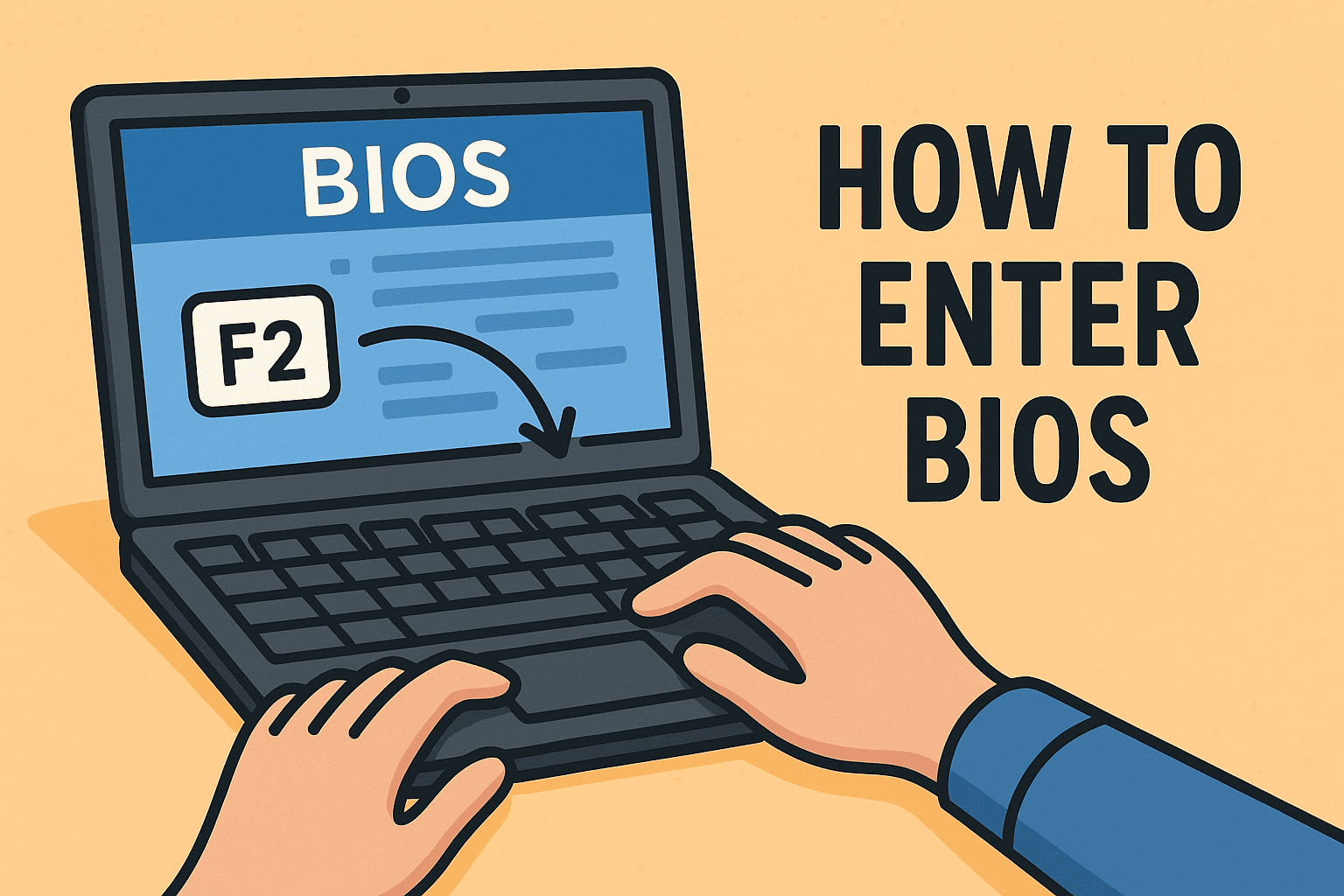
Ever needed to change boot settings, enable virtualization, or reset a forgotten admin password? You’ll need to know how to enter BIOS to get there. BIOS (Basic Input/Output System) and its modern successor UEFI control low-level system settings, and knowing how to access them is crucial for IT managers, cybersecurity experts, and enterprise teams. In…
How to Enter BIOS: A Complete Guide for Tech & Security Leaders