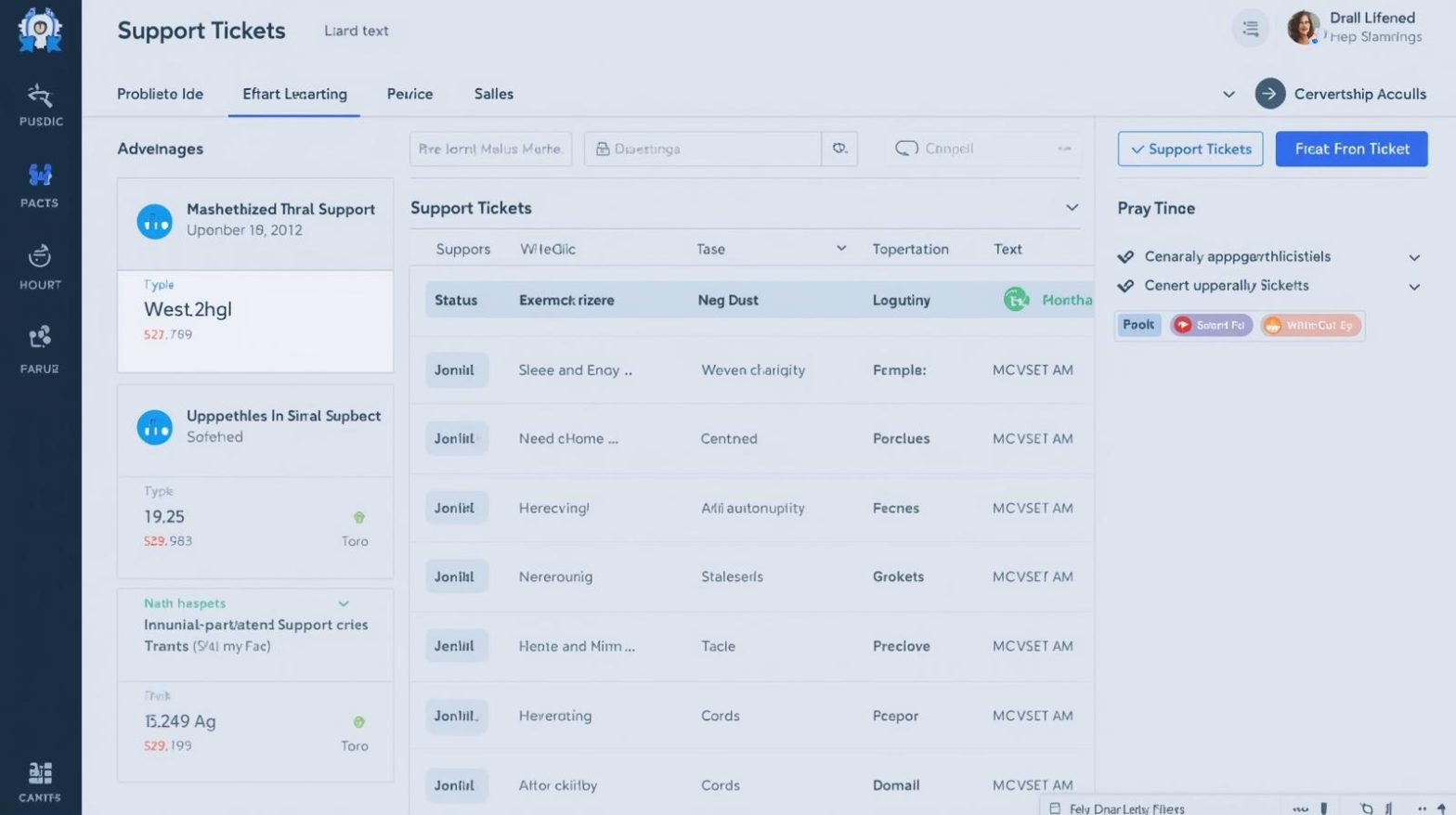
As technology environments grow more distributed and security threats increase, IT teams are looking more closely at the tools they use to manage, monitor, and secure devices. This is where the discussion of RMM vs MDM becomes essential. Both Remote Monitoring and Management (RMM) and Mobile Device Management (MDM) play critical roles in endpoint oversight,…
RMM vs MDM: Understanding the Difference for Modern IT Environments