Endpoint Attack Surface Reduction for Modern IT Security
Updated on March 23, 2026, by ITarian
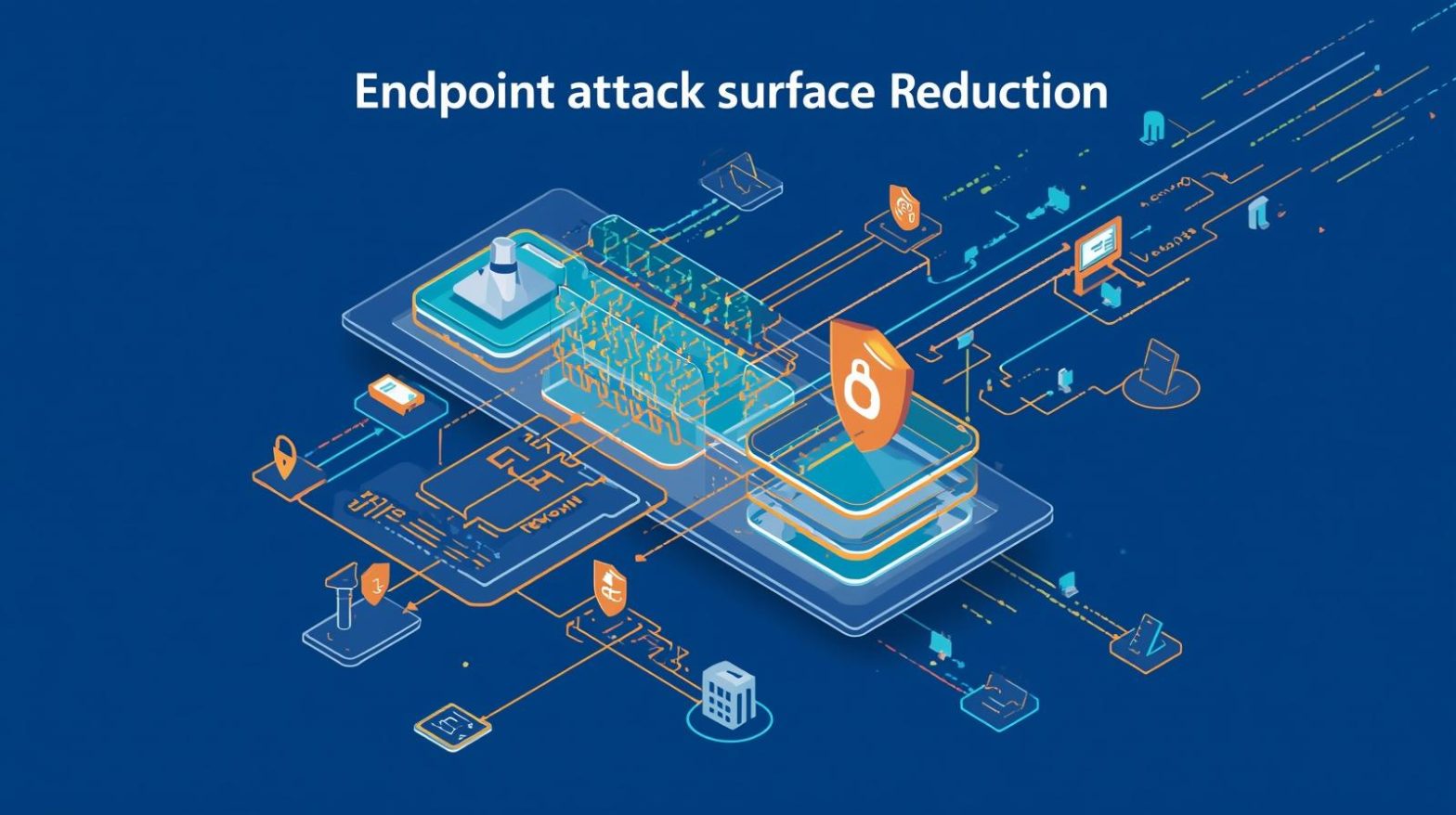
Every endpoint in your organization—laptops, servers, mobile devices—can become an entry point for cyber threats. The question is, how many of these entry points are truly secured? Endpoint attack surface reduction is a critical strategy that helps organizations minimize vulnerabilities and reduce exposure to cyberattacks. In an era where remote work, cloud adoption, and connected devices are expanding rapidly, unmanaged endpoints can quickly turn into security risks. For IT managers, cybersecurity professionals, and business leaders, reducing the attack surface is essential to maintaining control, protecting sensitive data, and ensuring operational continuity. Let’s explore how endpoint attack surface reduction works and why it’s a top priority for modern enterprises.
What is Endpoint Attack Surface Reduction
Endpoint attack surface reduction refers to the process of minimizing the number of potential entry points that attackers can exploit within endpoint devices. It involves identifying vulnerabilities, eliminating unnecessary services, and enforcing strict security controls.
This approach focuses on reducing exposure rather than just responding to threats. By limiting what attackers can access, organizations significantly lower the risk of successful breaches.
Key elements of endpoint attack surface reduction include:
-
Removing unused applications and services
-
Restricting user privileges
-
Controlling application execution
-
Enforcing patch management
-
Monitoring endpoint activity
For organizations managing large IT environments, this strategy is essential for maintaining a strong security posture.
Why Endpoint Attack Surface Reduction Matters for Cybersecurity
Cyber threats are becoming more sophisticated, targeting endpoints as the weakest link in the security chain. Endpoint attack surface reduction helps organizations stay ahead of these threats.
Reduced Risk of Breaches
By eliminating unnecessary access points, organizations reduce the chances of attackers exploiting vulnerabilities.
Improved Visibility
Security teams gain better insight into endpoint activity, making it easier to detect anomalies.
Faster Threat Mitigation
With fewer vulnerabilities, incident response becomes more efficient and effective.
Enhanced Compliance
Reducing the attack surface helps organizations meet regulatory requirements and security standards.
Lower Operational Costs
Preventing breaches reduces the financial impact of security incidents.
For CEOs and founders, this translates into stronger business resilience and reduced risk exposure.
Key Components of Endpoint Attack Surface Reduction
A successful strategy requires focusing on several critical components.
Application Control
Limiting which applications can run on endpoints prevents unauthorized or malicious software from executing.
Privilege Management
Restricting user permissions ensures that employees only have access to what they need.
Patch Management
Keeping systems updated reduces vulnerabilities that attackers can exploit.
Network Segmentation
Separating networks limits the spread of threats if an endpoint is compromised.
Endpoint Monitoring
Continuous monitoring helps detect suspicious activity in real time.
These components work together to create a layered defense against cyber threats.
Common Threats Addressed by Attack Surface Reduction
Endpoint attack surface reduction helps mitigate various types of cyber threats.
Malware and Ransomware
Limiting application execution reduces the risk of malware infections.
Phishing Attacks
Restricting access and monitoring behavior helps detect and prevent phishing attempts.
Zero-Day Exploits
Reducing vulnerabilities minimizes the impact of unknown threats.
Insider Threats
Privilege management and monitoring help prevent unauthorized actions by internal users.
Unpatched Software Exploits
Regular updates eliminate known vulnerabilities.
By addressing these threats, organizations can significantly strengthen their security posture.
Benefits of Endpoint Attack Surface Reduction Across Industries
Different industries benefit from this approach in unique ways.
Healthcare
-
Protects sensitive patient data
-
Ensures compliance with regulations
-
Reduces risks from outdated systems
Finance
-
Secures financial transactions
-
Prevents fraud
-
Maintains compliance with strict standards
Retail
-
Protects customer data
-
Ensures secure payment systems
-
Reduces downtime
Manufacturing
-
Secures operational technology
-
Prevents production disruptions
-
Enhances system reliability
Education
-
Protects student data
-
Secures remote learning environments
-
Manages large device networks
For IT leaders across industries, reducing the attack surface is key to maintaining secure operations.
Challenges in Implementing Endpoint Attack Surface Reduction
While the benefits are clear, organizations may face challenges during implementation.
Complexity of IT Environments
Managing diverse endpoints across multiple locations can be difficult.
Legacy Systems
Older systems may not support modern security controls.
User Resistance
Employees may resist restrictions that limit their access or workflows.
Integration Issues
Security tools must integrate seamlessly with existing systems.
Resource Constraints
Implementing and managing security measures requires time and expertise.
Overcoming these challenges requires careful planning and the right tools.
Best Practices for Effective Endpoint Attack Surface Reduction
To maximize the effectiveness of your strategy, follow these best practices.
Conduct Regular Risk Assessments
Identify vulnerabilities and prioritize remediation efforts.
Implement Least Privilege Access
Ensure users only have the permissions they need.
Use Automation Tools
Automate patch management, monitoring, and reporting.
Enforce Application Whitelisting
Allow only approved applications to run on endpoints.
Monitor Continuously
Use real-time monitoring to detect and respond to threats.
Educate Employees
Train staff on security best practices to reduce human error.
These practices help create a strong foundation for endpoint security.
Role of Automation in Attack Surface Reduction
Automation plays a critical role in managing endpoint security efficiently. It reduces manual effort and improves response times.
Key benefits of automation include:
-
Real-time vulnerability detection
-
Automated patch deployment
-
Continuous monitoring
-
Faster incident response
-
Reduced human error
Automation tools integrate with security platforms, enabling organizations to manage endpoints at scale.
How to Implement Endpoint Attack Surface Reduction Successfully
A structured approach ensures effective implementation.
Step 1: Identify Assets
Create an inventory of all endpoint devices.
Step 2: Assess Risks
Evaluate vulnerabilities and prioritize high-risk areas.
Step 3: Apply Security Controls
Implement measures such as application control and privilege management.
Step 4: Monitor and Analyze
Track endpoint activity and identify anomalies.
Step 5: Optimize Continuously
Refine strategies based on performance and emerging threats.
Step 6: Align with Business Goals
Ensure security measures support overall business objectives.
Following these steps helps organizations build a robust security framework.
Future Trends in Endpoint Attack Surface Reduction
The field of cybersecurity is evolving rapidly, and attack surface reduction is no exception.
AI-Powered Security
Artificial intelligence enables predictive threat detection and automated responses.
Zero Trust Architecture
Organizations are adopting zero trust models to enhance security.
Cloud-Based Endpoint Security
Cloud solutions provide scalability and flexibility.
Integration with EDR and XDR
Advanced detection and response tools enhance endpoint security.
Increased Focus on Remote Work Security
As remote work grows, securing endpoints becomes even more critical.
Staying ahead of these trends is essential for maintaining a competitive edge.
Actionable Tips to Reduce Your Endpoint Attack Surface
If you’re ready to strengthen your endpoint security, consider these practical tips:
-
Remove unused software and services
-
Regularly update systems and applications
-
Limit user privileges
-
Implement application control policies
-
Monitor endpoint activity continuously
-
Use automation tools for efficiency
These steps help reduce vulnerabilities and improve overall security.
Frequently Asked Questions
Q1: What is endpoint attack surface reduction?
It is the process of minimizing vulnerabilities on endpoint devices to reduce the risk of cyberattacks.
Q2: Why is attack surface reduction important?
It helps prevent breaches by limiting the number of entry points attackers can exploit.
Q3: What tools are used for attack surface reduction?
Common tools include endpoint security platforms, patch management systems, and monitoring tools.
Q4: Can small businesses benefit from this strategy?
Yes, reducing the attack surface helps organizations of all sizes improve security and reduce risks.
Q5: How often should organizations review their attack surface?
Regular reviews should be conducted to identify new vulnerabilities and ensure ongoing protection.
Final Thoughts
Endpoint attack surface reduction is a vital strategy for organizations looking to strengthen their cybersecurity defenses. By minimizing vulnerabilities, enforcing strict controls, and leveraging automation, businesses can significantly reduce their risk exposure. For IT managers, cybersecurity professionals, and business leaders, this approach not only enhances security but also supports operational efficiency and long-term growth. As cyber threats continue to evolve, organizations that prioritize attack surface reduction will be better equipped to protect their assets and maintain resilience.

 (1 votes, average: 4.00 out of 5)
(1 votes, average: 4.00 out of 5)