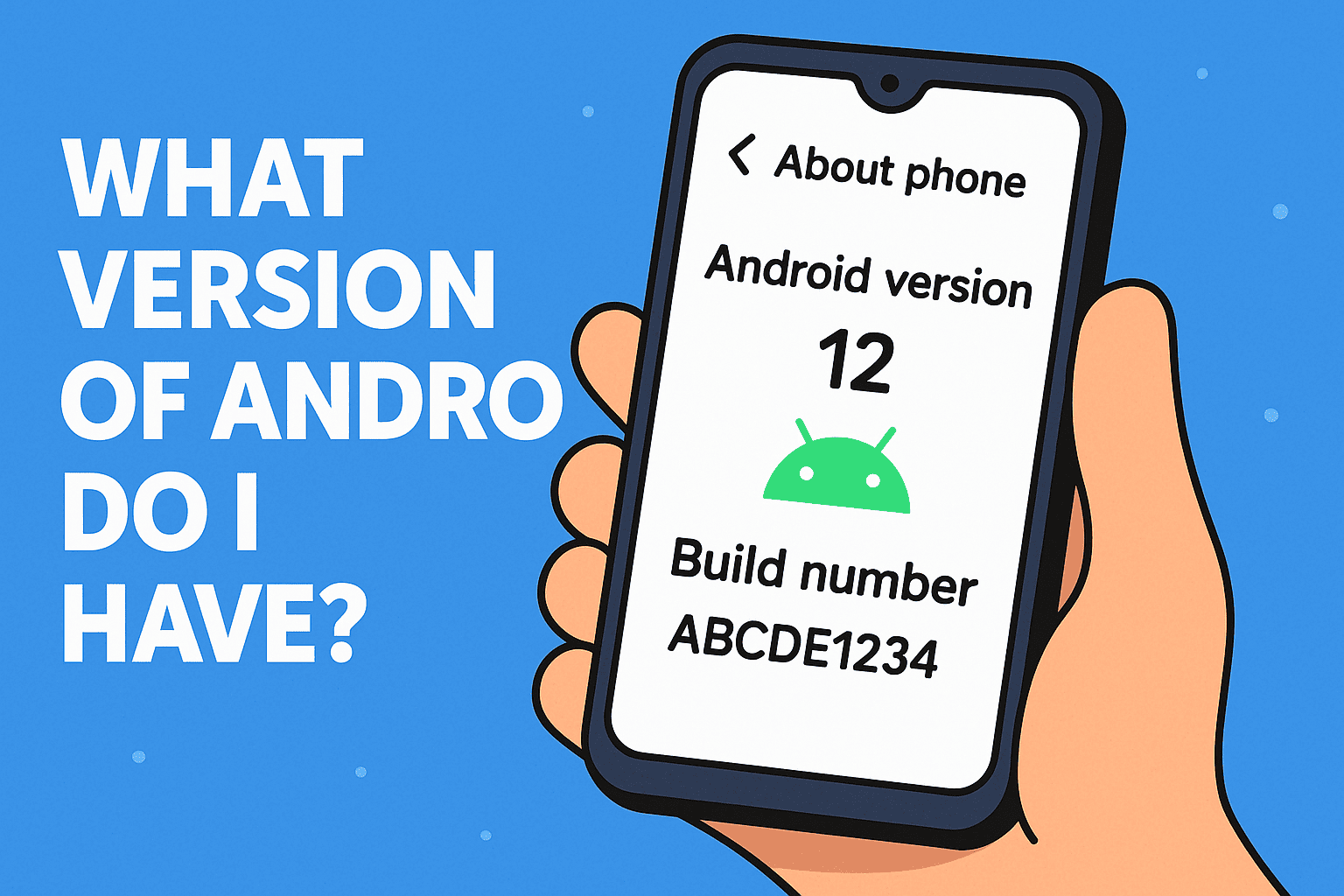
Have you ever stopped and asked yourself, what version of Android do I have? If you’re an IT manager, cybersecurity analyst, or tech-savvy CEO, you probably know that Android version number isn’t just a fun fact—it’s a serious security checkpoint. Your device’s OS version determines app compatibility, vulnerability exposure, and even compliance with internal IT…
The Importance of Knowing Your Android Version